Ransomware Rampage: 12 Organizations Breached were disclosed in a Single Day. What March 26, 2026, Reveals About Your Defense Gaps.

The Day Six Ransomware Groups Moved at Once
Today, it was disclosed that threat intelligence feeds tools that monitor cyber risks showed confirmed attacks across 12 organizations spanning healthcare, higher education, government, hospitality, and logistics. The attackers were not acting alone: six separate ransomware groups worked simultaneously. The groups, named NightSpire, Medusa, ALP-001, INC_RANSOM, Qilin, and NasirSecurity, acted in coordination. This was not random; it showed that cybercriminals are collaborating at a large, organized scale.For CISOs and IT Directors, this week underscores the risks of relying on point-in-time assessments, periodic patching, and siloed incident response. CISO leadership now requires continuous adaptation. Has your organization evolved its defense to match the threat?
Who Was Hit And Why It Matters to You
The confirmed victims reported included: Anbogen, Cape May County (NJ), Eastex Labs, Esprinet, Glenmark Pharma, HLF Goslar, LiveCH, Lorain County Community College, LP Kolding, Noi Hotels, Pulpdent, and UAE Customs.Look carefully at that list. You'll notice it's not dominated by large enterprises with assumed weak security postures. It's a deliberately cross-sector portfolio of targets, a county government, a community college, a pharmaceutical company, a hospitality group, and a dental manufacturer. These are mid-market and public sector organizations that share a common profile:
- Lean IT/security teams relative to the attack surface.
- Aging or mixed legacy/cloud infrastructure
- Inconsistent patch cycles under operational pressure
- Third-party vendor dependencies that expand the attack surface
This is not accidental targeting. Many Ransomware syndicates in 2026 run Ransomware-as-a-Service (RaaS) models with affiliate programs. The diversity of victims on any given day reflects the breadth of affiliates scanning for opportunistic entry points, unpatched systems, exposed RDP, compromised credentials from prior breaches, and vulnerable third-party supply chains.
Industry Best Practice Note: Sector-specific targeting has increasingly given way to opportunistic mass scanning. No organization with annual revenue under $500M should assume it is below the target threshold.
The Vulnerability Pipeline Feeding These Attacks
The multi-organization breach wave didn't happen in a vacuum. In the weeks leading up, several critical vulnerabilities created the pipeline that ransomware groups exploited.
CVE-2026-33017: The Langflow Zero-Day That Took 20 Hours to Weaponize
On March 17, 2026, security researchers publicly disclosed CVE-2026-33017, a critical vulnerability that allows attackers to run their own code remotely in Langflow. Langflow is a widely used, free framework for building automated AI processes and pipelines for large language models (LLMs). Within 20 hours of disclosure, real-world attacks exploiting it were confirmed.This is not a typo. Twenty hours.For organizations running AI development environments, this represents a paradigm-breaking threat reality. Langflow's rapid adoption in enterprise AI labs means the exposure surface is significant, and many organizations don't even know they're running it (introduced through developer tooling, internal AI chatbot projects, or vendor-supplied software).
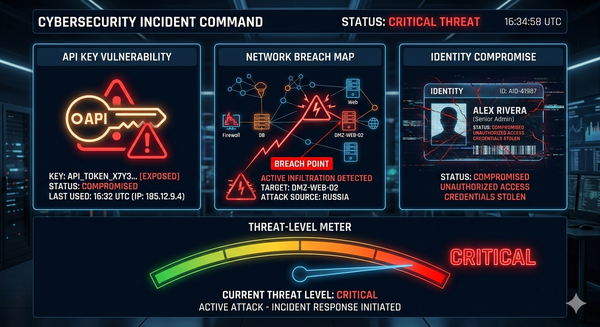
CVE-2026-20131: Cisco Secure Firewall Exploited by Interlock Ransomware
Adding to the pressure, CVE-2026-20131, a vulnerability in Cisco Secure Firewall, was confirmed as actively exploited by the Interlock ransomware group. The painful irony of ransomware groups targeting security tools themselves should not be lost on any technical leader. If your perimeter defense, which acts as a boundary to protect your internal network, is itself the way in, traditional layered security assumptions collapse.
PolyShell: The E-Commerce Skimming Campaign Scaling Fast
A third active threat vector emerged: the PolyShell security flaw affecting websites running Magento Open Source and Adobe Commerce. By March 26, more than 50 different internet addresses had been detected searching for stores with this flaw, with the first hacking attempts traced back to March 19. Alarmingly, the flaw put 56.7% of unprotected stores at risk as of the report date.Organizations in retail, e-commerce, or any sector running these platforms, including those with third-party vendors, must act immediately.
Microsoft Patch Tuesday March 2026: 79 Vulnerabilities, Two Zero-Days
In addition to everything above, Microsoft’s March 2026 Patch Tuesday update fixed 79 software vulnerabilities (security flaws), including two particularly dangerous ones, known as zero-days, that could allow attackers to gain extra permissions or disrupt services.Seventy-nine patches in a single month is a crushing operational demand for most IT teams. Prioritization based solely on CVSS scores is no longer sufficient; organizations need threat-informed prioritization that accounts for active exploitation status, asset criticality, and business impact.
A Framework for Ransomware Defense in 2026
March 26 revealed critical gaps. CISOs and IT Directors should drive the following framework:Go beyond CVSS (Common Vulnerability Scoring System) score rankings. Use up-to-date threat intelligence feeds (like CISA's Known Exploited Vulnerabilities catalog or commercial security services) to set patch priorities based on:
- Active exploitation in the wild
- Presence in your specific environment
- Asset criticality and blast radius if compromised
AAny CVE listed in the CISA KEV catalog should be treated as a 72-hour mandatory patch cycle, regardless of your standard patch window.2. Audit Your AI Development Toolchain Immediately.Langflow CVE-2026-33017 highlights a blind spot. CISOs should immediately audit all AI/ML tools deployed by development, labs, and vendors to ensure inventory and control.
- All AI/ML frameworks are deployed across developer workstations, lab environments, and cloud instances.
- Open-source LLM (large language model) orchestration tools such as Langflow, tools built on LangChain, AutoGen, or similar frameworks
- Vendor-supplied AI capabilities embedded in SaaS platforms
Mandate a full audit of AI infrastructure now. Assign owners, set deadlines, and report findings to leadership. Waiting increases risk—initiate this as a top-priority task.
3. Validate Perimeter Security Infrastructure — Don't Assume It's Protecting You
The attack on Cisco Secure Firewall by Interlock ransomware shows an important fact: security hardware and software are not automatically safe. Make sure your patching process includes all security devices, Security Information and Event Management (SIEM) software, Endpoint Detection and Response (EDR) tools, and network infrastructure. Regularly (at least every three months), check that all your security devices have the latest software and firmware updates.
4. Operationalize Your Incident Response Plan Before You Need It
Ensure incident response plans are operationalized: regularly test, assign roles, equip, and practice under realistic conditions. Take the following actions:
- Conduct a tabletop exercise simulating a ransomware deployment with lateral movement.
- Validate backup integrity and recovery time objectives (RTO) against business continuity requirements.
- Ensure out-of-band communication channels are in place for when primary systems are compromised.
- Define decision authority clearly: who authorizes isolation of production systems at 2 AM?
5. Tighten Third-Party and Supply Chain Risk
Instruct risk, compliance, and procurement to review Tier 1 vendor security within 30 days. Update contracts to require 24-hour incident notification and enforce strict privilege control. Do not delay mitigation steps.
- Annual security assessments of all Tier 1 vendors
- Contractual incident notification requirements (< 24 hours)
- Principle of least privilege for all third-party access
The Broader Threat Context: Ransomware Groups Are Running Enterprises
NightSpire, Medusa, INC_RANSOM, and Qilin are not amateur operations. These ransomware groups operate like organized businesses, with specialized teams for research, recruiting partners (affiliates), staff who handle ransom negotiations, and even public relations efforts to pressure victims into paying. In the weeks before March 26:
- TELUS Digital was attacked by ShinyHunterz on March 11, 2026, resulting in the compromise of 1 petabyte of data, including source code, FBI background checks, and Salesforce data.
- Malaysia Airlines suffered a Qilin ransomware attack that compromised passenger booking records, personnel files, vendor contracts, and internal communications.
The same groups targeting global enterprises are conducting parallel campaigns against your peers in the mid-market. The affiliate model has democratized these attack capabilities, raising risk for CISOs regardless of organization size.
Common Mistakes That Create These Opportunities
Drawing from patterns across March 2026 incidents, here are the most common organizational failures enabling ransomware success:
- Treating patch management as a simple monthly task instead of a risk-based, ongoing process
- Ignoring security tooling as a patch target — firewalls, EDR agents, and SIEM components need patching too
- Underinvesting in AI/ML asset inventory — not knowing what's running in your environment is a critical gap.
- Backup validation theater — running backups without regularly testing restoration under realistic conditions
- Assuming compliance with frameworks like HIPAA, PCI-DSS, and SOC 2 ensures security, when in reality these are regulatory standards that do not always address new cyber threats; attackers are not bound by audit cycles.
Risk Consideration: The Stryker Healthcare Warning
One more data point from March 2026 deserves attention: a cyberattack on Stryker, a major medical technology company, was linked to an Iran-aligned hacktivist group. This reflects an increasingly blurred line between financially motivated ransomware and geopolitically motivated cyber operations. Healthcare and critical infrastructure organizations must now account for nation-state-aligned threat actors in their risk models, not just criminal RaaS groups.
What This Means for Your Security Investment Thesis
The events of March 26, 2026, carry a clear message for budget conversations and board-level security discussions: reactive security spending costs more than proactive investment. The average ransomware recovery cost, factoring in downtime, data recovery, legal exposure, regulatory penalties, and reputational damage, consistently exceeds the cost of the controls that would have prevented the incident.The question is no longer whether your organization will be targeted. It's whether your defenses will make you a costly-enough target that threat actors move on to easier victims.
Is Your Security Posture Ready for 2026's Threat Reality?
If March 26, 2026, has you asking hard questions about your organization's resilience, that's exactly the right response. The organizations that weather ransomware campaigns are not those that got lucky; they're those that built and tested disciplined, intelligence-driven security programs.
Sources
- Cyberpress.org "Microsoft Patch Tuesday March 2026: 79 Vulnerabilities Fixed" https://cyberpress.org/microsoft-patch-79-vulnerabilities/
- The Hacker News "Critical Langflow Flaw CVE-2026-33017 Exploited in the Wild" https://thehackernews.com/2026/03/critical-langflow-flaw-cve-2026-33017.html
- GlobeNewswire "CTERA Named a 2025 Gartner Peer Insights Strong Performer for Hybrid Cloud Storage" (March 26, 2026) https://www.globenewswire.com/news-release/2026/03/26/3262946/0/en/CTERA-Named-a-2025-Gartner-Peer-Insights-Strong-Performer-for-Hybrid-Cloud-Storage.html
- HPE Newsroom "HPE Introduces Sweeping Security Advancements to Secure AI Adoption and Strengthen Enterprise Resiliency" (RSA Conference, March 23–26, 2026) https://www.hpe.com/us/en/newsroom/press-release/2026/03/hpe-introduces-sweeping-security-advancements-to-secure-ai-adoption-and-strengthen-enterprise-resiliency.html
- CVE Details March 2026 Vulnerability List https://www.cvedetails.com/vulnerability-list/year-2026/month-3/March.html
- Digital Applied "March 2026 AI Roundup" https://www.digitalapplied.com/blog/march-2026-ai-roundup-month-that-changed-everything
- The Hacker News General Cybersecurity Coverage (March 2026) — https://thehackernews.com/