Three Cybersecurity Crises Shaking Enterprise IT This Week. And What Your Team Should Do.
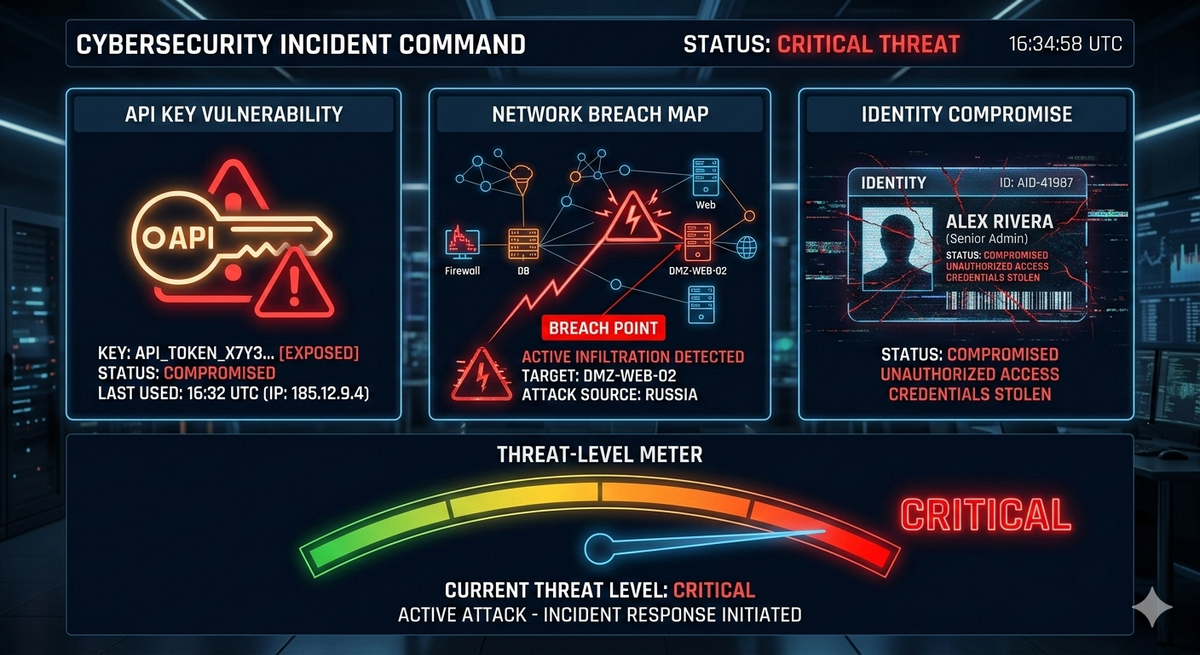
In the span of days, its been reported three distinct cybersecurity incidents have expose fundamental weaknesses in how organizations manage API credentials, network infrastructure, and third-party identity verification. Each one, on its own, would warrant an emergency briefing. Together, they paint a picture of systemic risk that demands immediate executive attention.
Here's what happened, why it matters, and most importantly, what your team should be doing about it right now.
Exposed Google API Keys Are Granting Unauthorized Access to Gemini AI
For over a decade, Google told developers that API keys were "not secrets." Then Gemini changed the rules.
Security researchers at Truffle Security discovered that millions of existing Google API keys, many created years before Gemini existed, were actively accessing Google's Gemini AI services. Keys that were originally scoped to Maps or Translate suddenly unlocked access to AI capabilities, uploaded files, and cached content. Truffle Security's scan of public internet pages turned up nearly 3,000 exposed keys, including one of Google's own, dating back to February 2023.
The implications are severe. Any attacker scraping publicly exposed keys can now access Gemini-powered data, exfiltrate uploaded files, and rack up charges on the victim's billing account. Organizations that followed Google's original guidance, treating API keys as low-sensitivity identifiers, are now sitting on a retroactive privilege escalation they never anticipated.
Google has responded by defaulting new keys created through AI Studio to Gemini-only access and blocking known leaked keys. But the burden falls on every organization that has ever deployed a Google API key.
What You Should Do
- Audit immediately. Inventory every Google API key your organization has issued. Use secret scanning tools such as TruffleHog, GitLeaks, or cloud-native secret managers to identify keys exposed in public repositories, documentation, or client-side code.
- Rotate and restrict. Rotate all keys that cannot be confirmed as unexposed. Apply API key restrictions to limit each key to the specific services and IP ranges it requires.
- Implement secret management infrastructure. If your organization still stores API keys in environment variables, configuration files, or code repositories, this incident is the catalyst to adopt a centralized secrets management platform (such as HashiCorp Vault, AWS Secrets Manager, Azure Key Vault, or an equivalent).
- Monitor billing anomalies. Set up alerting on your Google Cloud billing account for unexpected Gemini API usage — this is often the first indicator of key compromise.
Cisco SD-WAN Zero-Day (CVE-2026-20127) Is Under Active Exploitation
This one is as bad as it gets. CVE-2026-20127 is a CVSS 10.0 authentication bypass vulnerability in Cisco Catalyst SD-WAN Controller and Manager that allows unauthenticated remote attackers to obtain full administrative privileges. CISA has issued Emergency Directive ED 26-03, classifying the vulnerability as an "unacceptable risk" and mandating that federal agencies patch by February 27, 2026.
What makes this particularly alarming is the timeline. The threat actor, tracked as UAT-8616, has been exploiting this vulnerability since 2023, meaning organizations have been unknowingly compromised for years. Post-exploitation activities include installing rogue peers, gaining root access, and deliberately downgrading software to maintain persistence across patching cycles. This is sophisticated, patient, and methodical, consistent with a state-sponsored operation.
If your organization runs Cisco Catalyst SD-WAN infrastructure, this is not a "patch during the next maintenance window" situation. This is a stop-what-you-are-doing-and-respond situation.
What You Should Do
- Patch immediately. Apply the released Cisco patches to all affected SD-WAN Controller and Manager instances — both on-premises and in the cloud. Do not wait for your next scheduled maintenance cycle.
- Hunt for compromise indicators. Assume breach until proven otherwise. Examine your SD-WAN infrastructure for rogue peer configurations, unauthorized administrative accounts, unexpected software version changes, and anomalous management plane traffic. CISA's supplemental guidance for ED 26-03 provides specific hunt procedures.
- Segment management access. If you have not already implemented out-of-band management for SD-WAN controllers, do so now. Restrict management plane access to dedicated management VLANs with multi-factor authentication.
- Review your SD-WAN architecture. This incident underscores the risk of centralized control planes in software-defined networking. Evaluate whether your architecture provides adequate segmentation between the control plane, data plane, and management plane per Zero Trust principles by the NIST SP 800-207 guidance.
- Engage threat intelligence. If you identify indicators of UAT-8616 activity, immediately escalate to CISA and your incident response provider. The extended dwell time means forensic scoping will be critical.
IDMerit KYC Breach Exposes 1 Billion Personal Records Across 26 Countries
The third incident is a lesson in supply chain risk that extends far beyond traditional IT infrastructure. IDMerit, an AI-powered digital identity verification provider serving the fintech sector, exposed approximately 1 billion personal records through an unprotected MongoDB database. The exposed data includes full names, addresses, national ID numbers, dates of birth, phone numbers, email addresses, and KYC/AML verification logs spanning 26 countries.
The geographic scale is staggering: Cybernews research reported 203+ million U.S. records, 124 million from Mexico, 72 million from the Philippines, and tens of millions each from Germany, Italy, and France. The breach was discovered by Cybernews researchers on November 11, 2025, and the database was reportedly secured the following day. Still, public disclosure did not come until February 18, 2026, a 99-day gap that raises serious questions about notification obligations under GDPR, CCPA, and other privacy regulations.
For any organization that relied on IDMerit for identity verification, the downstream risk is substantial. Exposed KYC data does not just enable identity theft; it enables attackers to bypass KYC processes at other institutions by presenting stolen, verified identity packages. This is a supply chain compromise of the identity infrastructure itself.
What You Should Do
- Determine your exposure. Contact IDMerit directly to determine whether your customer data was included in the exposed dataset. Do not assume you are unaffected simply because you are not a direct IDMerit customer; your KYC vendor may use IDMerit as an upstream provider.
- Enhance identity verification controls. Layer additional verification steps beyond document-based KYC. Behavioral biometrics, liveness detection, and cross-referencing against multiple authoritative sources reduce reliance on any single verification provider.
- Assess your third-party risk program. This breach exposes a common blind spot: organizations often vet their direct vendors but not their vendors' vendors. Your third-party risk management framework should require vendors to disclose subprocessor relationships and demonstrate security controls at each tier.
- Monitor for identity fraud indicators. Alert your fraud detection teams to watch for account creation attempts using identity packages that match the IDMerit dataset profile, particularly from the most affected geographies.
- Review regulatory obligations. If your organization is subject to GDPR, CCPA, or sector-specific privacy regulations, consult legal counsel on your notification obligations related to this third-party breach.
The Common Thread: Assumed Trust Is the Enemy
These three incidents share a root cause that goes beyond any single vulnerability or misconfiguration. Each one represents a failure of assumed trust:
Google assumed API keys were low-risk credentials. Organizations assumed their SD-WAN control planes were secure because they were protected by vendor authentication. Financial institutions assumed their KYC providers maintained adequate database security.
The lesson is not that trust is bad; it is that trust must be continuously verified. This is the operational reality of Zero Trust architecture: not a product you purchase, but a discipline you practice across every layer of your technology stack.
A practical framework for this week:
- Credential layer: Treat every API key, token, and service account credential as a potential attack vector. Automate rotation, enforce least privilege, and scan continuously for exposure.
- Infrastructure layer: Assume control planes are targets. Segment management access, monitoring for anomalous administrative activity, and maintaining a threat-hunting capability are not just about perimeter defense.
- Supply chain layer: Map your critical data flows through third-party providers. Require security attestations, enforce contractual breach notification timelines, and maintain the ability to switch providers without catastrophic disruption.
Mistakes to Avoid
- Do not treat the Cisco patch as routine. With a three-year dwell time, patching alone is insufficient. You must hunt for an existing compromise.
- Do not assume your Google API keys are restricted. Legacy keys may have gained permissions that were never explicitly granted. Verify, don't assume.
- Do not rely on a single KYC vendor without contingency. Single points of failure in identity verification create systemic risk across your entire customer base.
- Do not delay executive communication. Each of these incidents carries board-level risk. Brief your leadership now, not after the next quarterly review.
What Comes Next
The convergence of these three incidents is not coincidental. It reflects the accelerating complexity of enterprise attack surfaces. AI services are expanding credential risk. Software-defined infrastructure is creating new attack vectors for the control plane. And the identity verification supply chain is becoming a target in its own right.
Organizations that treat these as isolated incidents to patch and forget will find themselves on the back foot when the next wave hits. Those that use them as a catalyst to mature their security posture, tightening credential management, hardening infrastructure control planes, and demanding accountability from their supply chain to achieve a measurably more resilient supply chain.
Sources
- Google API Keys / Gemini Exposure: Truffle Security Blog: Google API Keys Weren't Secrets, But Then Gemini Changed the Rules
- Cybernews: Old Google API Keys Grant Gemini Access
- Cisco CVE-2026-20127:CISA Emergency Directive ED 26-03: Hunt and Hardening Guidance for Cisco SD-WAN Systems
- The Hacker News: Cisco SD-WAN Zero-Day CVE-2026-20127
- Tenable: CVE-2026-20127 Analysis
- SecurityWeek: Cisco Patches Catalyst SD-WAN Zero-Day
- IDMerit KYC Data Breach:Cybernews: Global Data Leak Exposes Billion Records
- TechRadar Pro: Massive Global Data Breach Coverage
- Tom's Guide: 1 Billion Personal Records Exposed