When Nation-States Weaponize AI: Olympic DDoS Storms, Deepfake Zoom Calls, and the Malware That Learns
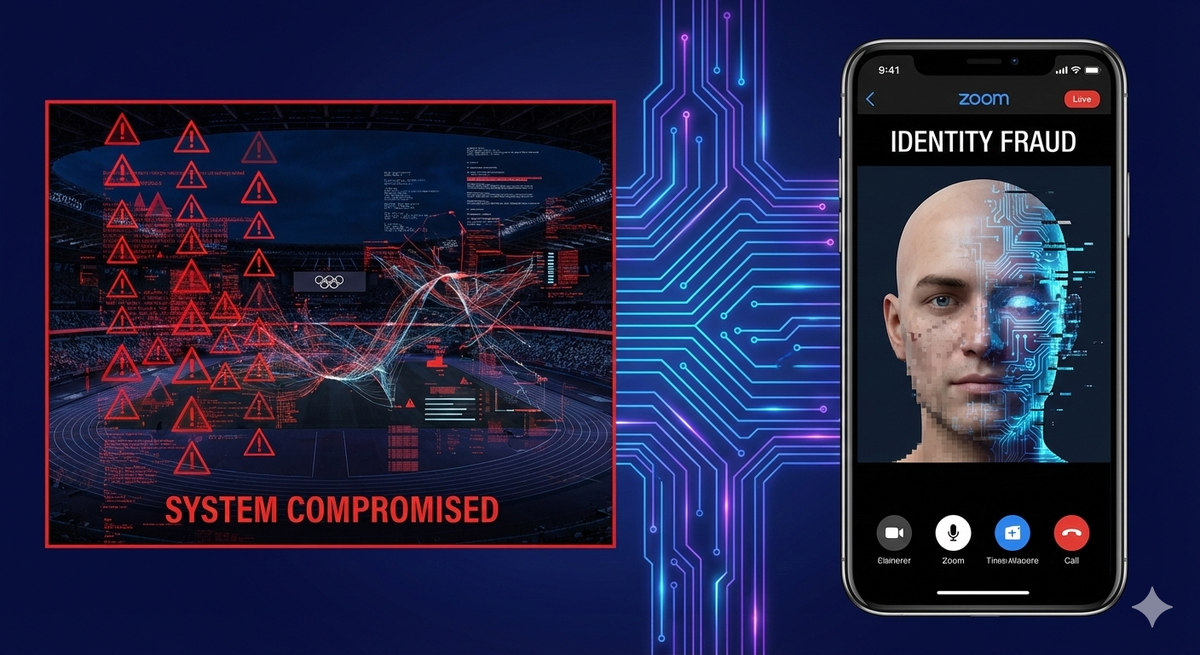
Recent news should prompt a reevaluation of threat modeling by every IT leader. A Russian hacktivist group has launched sustained DDoS campaigns targeting Olympic infrastructure. In another incident, North Korean operatives infiltrated cryptocurrency firms using deepfake video calls. Additionally, researchers have discovered the first Android malware that employs real-time generative AI, enabling it to adapt to any device it infects. Furthermore, South Korea has become the first country in the Asia-Pacific region to implement a comprehensive regulatory framework for AI.
Each of these developments is significant in its own right. Together, they indicate a clear turning point: AI has evolved from merely being a tool for defense to becoming a weapon, a lure, and a regulatory challenge simultaneously. Here's what occurred, what it means for your organization, and how you can respond.
Russia's NoName057(16) Turns the Winter Olympics Into a Cyber Battleground
As the 2026 Milan-Cortina Winter Olympics came to an end on February 22, the cyber component of the Games proved just as competitive as the sporting events themselves. The pro-Russian hacktivist group NoName057(16), which has been active since Russia's full-scale invasion of Ukraine in 2022, launched sustained distributed denial-of-service (DDoS) campaigns throughout the Games in response to Russia's exclusion as a competing nation.
Their targeting was extensive and intentional. NoName057(16) attacked Italian government infrastructure, the national Olympic committees of Lithuania, Poland, and Spain, tourism websites for Cortina d'Ampezzo, and Milan Malpensa Airport. They were not alone in their efforts. The BD Anonymous group also targeted two Italian airport websites, while the Z-Pentest Alliance and Server Killers claimed responsibility for attacks on Italian critical infrastructure. Approximately 120 targets were affected, including Italian consulates in Sydney, Toronto, and Paris, as well as hotels accommodating athletes in alpine resort areas.
Italy's Defensive Playbook
Italy's response to cybersecurity during the Games provides a model worth considering. For the first time, the Italian government established a round-the-clock cybersecurity command center in Rome to coordinate digital defenses across all venues and respond quickly to incidents. The National Cybersecurity Agency collaborated with approximately 6,000 police personnel and nearly 2,000 military staff deployed throughout the Games area, supported by drones, radar systems, and aircraft. As a result, the attacks did not lead to significant operational disruptions.
What This Means for Your Organization
The lessons learned extend beyond just sporting events. Any high-profile occasion your organization is involved with—such as industry conferences, product launches, regulatory milestones, or geopolitical flashpoints—can serve as a trigger for targeting. The group NoName057(16) mobilizes hundreds of volunteers and leverages a loosely connected network of servers to carry out relatively simple yet disruptive DDoS (Distributed Denial-of-Service) attacks. The barrier to entry for event-driven hacktivism is low, and the motivation behind these attacks is ideological rather than financial, making them harder to predict and negotiate.
Threat modeling frameworks should include event-driven scenarios alongside traditional technical vulnerability assessments. If your organization is connected to any geopolitically sensitive events, it's essential to pre-position DDoS mitigation strategies, coordinate with your Internet Service Provider (ISP) and Content Delivery Network (CDN) providers, and brief your incident response team on hacktivist tactics, techniques, and procedures (TTPs) before the event takes place.
North Korea's UNC1069: Deepfake Zoom Calls Meet Crypto Theft at Scale
Google's Mandiant threat intelligence team has published findings on UNC1069, a financially motivated threat actor from North Korea that has been active since at least 2018. This group has evolved into one of the most sophisticated social engineering operations targeting the cryptocurrency sector. Their latest campaign combines compromised Telegram accounts, spoofed Zoom meetings, AI-generated deepfake videos, and a ClickFix infection vector into a single, devastating attack chain.
The Attack Chain
The operation unfolds in several stages. First, UNC1069 compromises the Telegram account of a legitimate cryptocurrency executive. Using this trusted identity, the attacker contacts a target to build rapport before sending a Calendly link to schedule a meeting. This link directs the victim to a spoofed Zoom session hosted on the attacker's infrastructure.
During the call, the victim sees what appears to be a live video feed of a known industry figure, but it is either a deepfake or a recording secretly captured from a previous victim. The fake call simulates audio issues, prompting the victim to run "troubleshooting" commands on their system — a ClickFix attack that delivers the payload.
Forensic analysis of one intrusion revealed seven unique families of malware deployed on the victim's device, including previously undocumented tools named SILENCELIFT, DEEPBREATH, and CHROMEPUSH. These tools are designed to harvest passwords, browser data, session tokens, and cryptocurrency wallet credentials. Mandiant also confirmed that UNC1069 has utilized Google's Gemini AI for operational research and tool development.
Broader Context
Since 2023, UNC1069 has shifted its focus from traditional finance to Web3, engaging with centralized exchanges, DeFi platforms, software developers in financial institutions, and individuals in venture capital funds. This trend aligns with a broader pattern: Chainalysis reported that North Korean hackers stole $2.02 billion in cryptocurrency in 2025 alone, a 51% increase from the previous year. These attacks are not opportunistic; they are state-sponsored operations aimed at funding a nuclear weapons program.
Defensive Recommendations
Organizations in the cryptocurrency and financial services sectors should adopt out-of-band identity verification for any meetings initiated via messaging platforms. Never trust a video call at face value; always verify the participant's identity through a separate, pre-established channel before sharing sensitive information or executing any commands. Additionally, implement endpoint detection and response (EDR) solutions to monitor for patterns of command execution similar to ClickFix, and provide specific training for employees on deepfake social engineering scenarios.
PromptSpy: The First Android Malware That Uses Generative AI to Think on Its Feet
ESET researchers announced on February 19 the discovery of PromptSpy, the first known Android malware to use generative AI during execution. This is not a theoretical proof-of-concept; it is fully functional malware that leverages Google's Gemini AI to navigate infected devices, adapt to various screen layouts, and maintain persistence in ways traditional malware cannot.
How It Works
Traditional Android malware typically relies on hard-coded tap coordinates and UI selectors to navigate a device. However, this method frequently fails due to variations across different manufacturers, screen sizes, and Android versions.
PromptSpy addresses this issue by sending Gemini a natural-language prompt along with an XML dump of the current screen, which includes the text, type, and position of every UI element. Gemini analyzes this context and returns JSON instructions specifying exactly which action the malware should take and where to perform it. This interaction occurs iteratively until the malware secures a position in the device's recent apps list, effectively preventing the user from terminating it.
Capabilities and Distribution
PromptSpy deploys a VNC (Virtual Network Computing) module that grants operators full remote control of the infected device. This malware can collect device information, capture lock screen PINs and passwords, record screen unlock patterns, and take screenshots. It exploits Android Accessibility Services to prevent removal by overlaying transparent rectangles over the uninstall buttons. Additionally, it disguises itself as a banking app named "MorganArg," impersonating JPMorgan Chase, and is distributed through manipulated websites rather than official app stores. Currently, its targeting focuses on users in Argentina.
Why This Matters Beyond Mobile Security
PromptSpy marks a significant shift in how malware operates. By using a generative AI model to make navigation decisions on devices, malware authors have successfully addressed the fragmentation issue that has historically limited Android malware's reach. As noted by ESET researchers, this approach allows threat actors to adapt to almost any device, layout, or operating system version, greatly increasing the number of potential victims. This is the second AI-powered malware discovered by ESET, following PromptLock, the first known AI-driven ransomware identified in August 2025.
Google has announced that no apps containing this malware are available on Google Play, and Google Play Protect automatically safeguards users against known versions. However, organizations with a BYOD (Bring Your Own Device) policy or a mobile workforce should view this as a signal to reevaluate their mobile threat defense strategies.
South Korea's AI Basic Act: The Regulatory Template the World Is Watching
On January 22, 2026, South Korea's AI Basic Act took effect, marking the first comprehensive regulatory framework for artificial intelligence in the Asia-Pacific region. Although the law was passed in December 2024 and officially announced in January 2025, its enforcement date has just entered the news cycle, and the implications for global organizations are becoming clearer as compliance requirements are established.
Key Provisions
The Act mandates human oversight for "high-impact" AI systems, including applications in healthcare, energy, public services, and other areas that could significantly impact public safety or fundamental rights. Companies using AI in these sectors must ensure that humans remain active in decision-making.
Additionally, the Act outlines transparency requirements that obligate firms to inform users in advance when products or services utilize high-impact or generative AI. Companies must also clearly label any AI-generated content that could be mistaken for real information.
For foreign AI companies operating in South Korea, the law requires them to appoint a Korean representative. Furthermore, the legislation establishes both an AI safety research institute and an AI ethics committee.
The Compliance Gap
Here's the uncomfortable reality: a survey conducted by South Korea's Startup Alliance found that 98% of 101 local AI startups lack systems to comply with the law. Nearly half of these startups admitted to being unfamiliar with the law's details. Although the government has indicated a grace period of at least one year before imposing administrative fines—up to 30 million won (approximately $20,400) for labeling violations—the direction is clear.
What Global IT Leaders Should Prepare For
South Korea's framework is set to influence AI regulation across the Asia-Pacific (APAC) region and beyond. Organizations with international operations should begin by inventorying their AI deployments in accordance with the Act's high-impact classification criteria. They should also establish workflows for labeling AI-generated content, document human oversight mechanisms for automated decision-making systems, and ensure that their AI vendors have designated representatives in Korea if they operate in that market.
The EU AI Act and South Korea's AI Basic Act now serve as two pillars of a global regulatory framework. Organizations that build compliance infrastructure for one will be better positioned to adapt to the other — and to whatever regulations may arise in the future.
Common Mistakes to Avoid
Organizations most exposed to these developments tend to share recognizable patterns. They treat DDoS mitigation as a static configuration rather than adopting an event-driven posture. Many have not trained employees to recognize deepfakes or to conduct out-of-band identity verification. They often lack mobile threat defense beyond basic Mobile Device Management (MDM) enrollment. Furthermore, they tend to view AI regulation as a future concern rather than a current compliance obligation.
Actionable Steps for This Week
For Chief Information Security Officers (CISOs) and IT Directors, here are five priorities to address before Friday:
1. Review your DDoS mitigation posture.
If your organization is connected to geopolitically sensitive events or industries, confirm that your Content Delivery Network (CDN) and Internet Service Provider (ISP) scrubbing capabilities are both active and tested, rather than merely configured.
2. Implement out-of-band verification protocols
Any meeting request originating from a messaging platform should require identity confirmation through a separate channel before sensitive discussions proceed.
3. Assess your mobile threat defense
Given that traditional signature-based mobile detection is insufficient with the advent of AI-adaptive threats, evaluate solutions based on behavioral analysis and review your Bring Your Own Device (BYOD) policies.
4. Begin an inventory of AI deployments
Map every AI system within your environment against South Korea's high-impact classification criteria and the EU AI Act's risk tiers. This inventory will be necessary regardless of which jurisdiction takes the lead next.
5. Brief your executive team
The convergence of nation-state AI weaponization, adaptive malware, and emerging regulation constitutes a board-level risk narrative. Leadership needs to understand that these issues are interconnected; they represent a new operational reality.
The week of February 20–22, 2026, made one thing clear: adversaries have adopted AI faster than most defenders have responded. Closing this gap requires viewing AI not as a singular technological initiative but as a cross-cutting factor in threat modeling, employee training, mobile security, and regulatory compliance. Organizations that adapt as quickly as the evolving threats around them will thrive in this new environment.
Sources
- The Record — Italy Blames Russia-Linked Hackers for Winter Olympics Cyberattacks
- Intel 471 — Winter Olympics 2026: Hacktivism Surges Ahead of Protests and Suspected Sabotage
- Security Affairs — Pro-Russian Group NoName057(16) DDoS Attacks on Milano Cortina 2026
- Google Cloud Blog / Mandiant — UNC1069 Targets Cryptocurrency Sector with AI-Enabled Social Engineering
- The Hacker News — North Korea-Linked UNC1069 Uses AI Lures to Attack Cryptocurrency Organizations
- Dark Reading — North Korea's UNC1069 Hammers Crypto Firms With AI
- The Record — North Korean Hackers Targeted Crypto Exec with Fake Zoom Meeting, ClickFix Scam
- ESET / WeLiveSecurity — PromptSpy Ushers in the Era of Android Threats Using GenAI
- BleepingComputer — PromptSpy Is the First Known Android Malware to Use Generative AI at Runtime
- SecurityWeek — PromptSpy Android Malware Abuses Gemini AI at Runtime for Persistence
- Library of Congress — South Korea: Comprehensive AI Legal Framework Takes Effect
- Future of Privacy Forum — South Korea's New AI Framework Act
- U.S. International Trade Administration — South Korea AI Basic Act



